Formulator Cloud Version
Formulator Cloud Version is built on the Amazon Web Services’ (AWS) world-class cloud infrastructure, a mature cloud platform specifically designed for the unique scalability, security, compliance, privacy, and governance requirements of multiple enterprises. It is installed, maintained and upgraded by the Formulator Support Staff.
All data is encrypted and our application is available through secure login from any browser or mobile device anywhere in the world. Standard security is maintained by specific User. All data entered and modified is date and time stamped, the individual Used noted, providing a full audit trail.
Sold as a subscription service, billed monthly against your credit card.
Extensive use of AWS native services for scalability, processing, database, access control, file backup and multiple layers of securityKeep your data safe with layered safeguards to protect all your data stored in redundant, highly secure AWS data centersMaintain the highest standard of IT security without having to manage your own facilityEuropean hosting for European customersInternationalized platform for those doing business in multiple countries
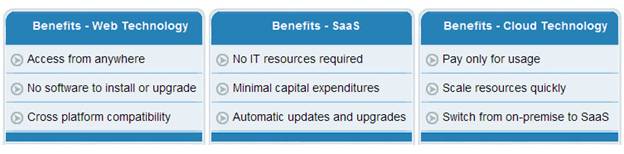
Formulator Cloud - Customer Benefits